In sensitive industries such as Aerospace, Nuclear Energy, Life Sciences, or Finance, cybersecurity has moved beyond a purely technical concern: it has become an issue of sovereignty, performance, and trust.
Critical infrastructures refer to the systems and activities essential to the smooth functioning of a country. Their failure would have severe consequences for both society and the economy. Today, these infrastructures are not only potential targets — they are under constant, increasingly intense attack.
These attacks rely on sophisticated campaigns combining espionage, sabotage, and supply chain disruption. They exploit 0-day vulnerabilities, targeted phishing, or discreet lateral movements between partners. Their goal: to establish a lasting foothold within strategic networks, harvest sensitive information, or disrupt operational continuity.
The consequences go far beyond technical incidents: they can trigger full-blown crises marked by halted operations, the collapse of strategic contracts, major financial losses, and regulatory sanctions. In some cases, disruptions can reach a local or even national scale, especially amid current geopolitical tensions that further amplify the threat.
Recent incidents illustrate the scale of the risk:
- France Travail (2024): massive data breach affecting over 43 million people
- Viamedis & Almerys (2024): 33 million insured individuals impacted following a third-party system compromise
- Collins Aerospace (2025): cyberattack on a check-in software system that disrupted part of air traffic
- Fortum (2025): European energy company facing daily cyber intrusions and physical breach attempts
In this context of heightened threats, interconnected supply chains, and stricter regulations, cybersecurity is emerging as a key driver of resilience, performance, and trust.
This article provides an analysis of the specific vulnerabilities affecting critical industries and outlines protection strategies tailored to their technical, operational, and regulatory constraints. To illustrate these dynamics, we focus on four high-stakes sectors: Aerospace, Nuclear Energy, Life Sciences, and Finance.
Current state of cyber vulnerabilities in sensitive sectors
Although the cyber threat is global, its manifestations differ from one industry to another.
Each sector combines specific technical architectures, operational constraints, and regulatory frameworks that shape its risk exposure.
Understanding these specifics is essential to design effective, business-aligned protection strategies.

Aerospace: cybersecurity at the heart of sovereignty issues
+600% — that’s the increase in ransomware attacks recorded in the aerospace sector between 2024 and 2025 (source: Thales, Cyber Threat Intelligence Report).
This striking figure highlights a clear trend: the aerospace industry has become one of the most targeted by cyberattacks.
Attacks can affect the entire value chain: manufacturers, airlines, airports, equipment suppliers and subcontractors, etc. In an environment where collaboration and technical exchanges are constant, the failure of a single player can weaken an entire ecosystem.
Multiple threats in an interconnected ecosystem
Attacks can affect the entire value chain — manufacturers, airlines, airports, equipment providers, and subcontractors. In a highly collaborative environment where technical data is constantly exchanged, a single weak link can jeopardize the entire ecosystem.
Ransomware and DDoS attacks account for more than 85% of reported incidents in the aerospace and defense sectors (source: Hub One, 2024).
They exploit both technical flaws — such as insecure protocols, outdated software, or poorly configured cloud and CI/CD systems — and human weaknesses through phishing or compromised suppliers.
The 2025 incident at Collins Aerospace is a prime example: a single attack on check-in software disrupted air traffic, illustrating how interdependencies magnify operational vulnerabilities.
Embedded software and critical aerospace systems often have long life cycles. Their updates, subject to complex validation processes, delay patching and extend exposure to risk.
The supply chain is another major weak point.
The industry depends on a dense network of partners with widely varying cybersecurity maturity levels. This interdependence creates a domino effect: one compromised supplier can endanger the whole ecosystem.
Effective protection thus requires a shared, coordinated cybersecurity approach embedded from project inception.
Protecting sensitive data and ensuring compliance
Industrial or state-sponsored espionage campaigns frequently target sensitive technologies and defense programs. Data exchanges between European states and industrial partners — particularly under NATO or joint programs — involve classified information flows and complex interconnections, multiplying potential attack vectors.
A notable example: in 2024, the SCAF (Future Combat Air System) program suffered intrusion attempts attributed to state-backed groups seeking to access critical design data.
In France, the industry operates under a strict regulatory framework, notably the IGI 1300 for classified information protection. While these requirements ensure strong safeguards, they can also slow internal processes and delay industrial programs.
The challenge lies in balancing compliance, operational performance, and agility against evolving threats.
Nuclear: strengthening security and continuity of operations
The nuclear sector epitomizes sovereignty and national continuity.
A cyberattack on a major group or facility could endanger not only a company but national security itself.
These organizations manage critical infrastructures whose malfunction could have severe economic, environmental, or human consequences.
Cybersecurity has therefore become a strategic pillar, on par with industrial safety and equipment maintenance.
Digital transformation: a new exposure surface
Historically focused on safety, the industry is undergoing a major digital transformation.
Automation, remote monitoring, and connected sensors (IoT, SCADA, control-command systems) boost efficiency — but every new connection widens the attack surface.
State-sponsored APT groups seek to establish persistent access within critical networks. These stealthy, long-term attacks exploit IT/OT convergence, where an office network breach can directly impact industrial operations.
The Stuxnet case (2010) remains emblematic: a malicious code sabotaged Iranian nuclear centrifuges while hiding its effects from operators. Though rare, such attacks paved the way for a new generation of threats targeting industrial control systems.
Securing critical systems under strict constraints
Nuclear industrial systems are often old and operate continuously, making it difficult to apply patches without downtime. This complicates updates and prolongs exposure to vulnerabilities.
Operators must therefore balance uninterrupted availability with reinforced security.
Supervised by ANSSI and the EU NIS2 directive, these infrastructures face stringent security and continuity requirements that now extend to their supply chains.
The key challenge: protect infrastructures while maintaining operational continuity in a highly sensitive environment.
Life Sciences: protecting data and ensuring compliance
Driven by innovation, the Life Sciences sector now faces a major new challenge: digital security.
Healthcare, pharmaceuticals, biotech, and research organizations are all undergoing rapid technological transformation, which mechanically increases their cyber exposure.
The widespread adoption of cloud platforms, connected clinical trials, and smart medical devices has turned laboratories and hospitals into prime cyber targets.
Highly sensitive data at the core of the threat
Data now represents the core value of the sector: clinical trial results, patient records, and pharmaceutical research. Any breach can have severe human, economic, and reputational consequences — from treatment disruption and data loss to espionage over strategic innovations.
Ransomware and data leaks are rising sharply, while the surge in connected medical equipment further heightens vulnerability.
The Change Healthcare incident (2024) illustrates this perfectly: a ransomware attack paralyzed billing systems across thousands of hospitals and led to the theft of sensitive health data.
A heavily regulated environment
The industry operates under strict frameworks such as the GDPR in Europe, FDA requirements in the U.S., and reinforced hosting and traceability obligations.
Organizations must balance innovation, data protection, and compliance. Even a minor breach can have heavy financial or legal repercussions.
The key to resilience lies in protecting data throughout its lifecycle — ensuring both patient trust and operational reliability.
Finance: ensuring trust and system stability
As a cornerstone of the global economy, the financial sector is naturally one of the most targeted by cyberattacks.
Its infrastructures — payment systems, stock exchanges, insurance, fintechs — are globally interconnected, meaning a single breach can have cascading effects across the entire system.
Cybersecurity has thus become essential for economic stability and public confidence.
Targeted attacks in a trust-based ecosystem
Frequent threats include ransomware, spear phishing, and CEO fraud, all targeting payment systems and technology providers.
One of the most notable early cases was that of Gilbert Chikli, considered a pioneer of CEO fraud. In the 2000s, he impersonated executives to obtain fraudulent fund transfers, exploiting human psychology and urgency — a reminder that trust itself is a vulnerability.
In a sector built on trust, human error and access misuse remain constant weak points.
Systemic risk and regulatory reinforcement
The financial system operates in cascades: an attack on a major institution, stock operator, or critical vendor can trigger chain reactions on national or even global scales.
This interdependence demands collective resilience and continuous coordination among all stakeholders.
Between the GDPR, NIS2 directive, and DORA regulation, the regulatory landscape is tightening to enhance systemic stability and crisis preparedness.
In such a deeply interconnected ecosystem, security depends above all on cooperation and shared vigilance.
A common trend: collective resilience as a necessity
Across Aerospace, Nuclear, Life Sciences, and Finance, organizations share similar structural vulnerabilities:
- Aging, interconnected systems
- Heavy dependence on supply chains
- Growing exposure from digital transformation
These factors call for an integrated cybersecurity approach — one that aligns technical protection, regulatory compliance, and operational continuity.
Resilience can no longer rely on isolated initiatives. It requires coordinated strategies involving stakeholders, suppliers, and regulatory authorities.
The following section explores these strategies, focusing on defense in depth, cyber culture, and collective crisis preparedness.
Protection strategies tailored to critical environments
For critical infrastructure operators, the goal is no longer to avoid every attack, but to ensure continuity and rapid recovery when incidents occur.
Cybersecurity must now be seen as a comprehensive process: anticipating threats, detecting them early, and limiting their impact.
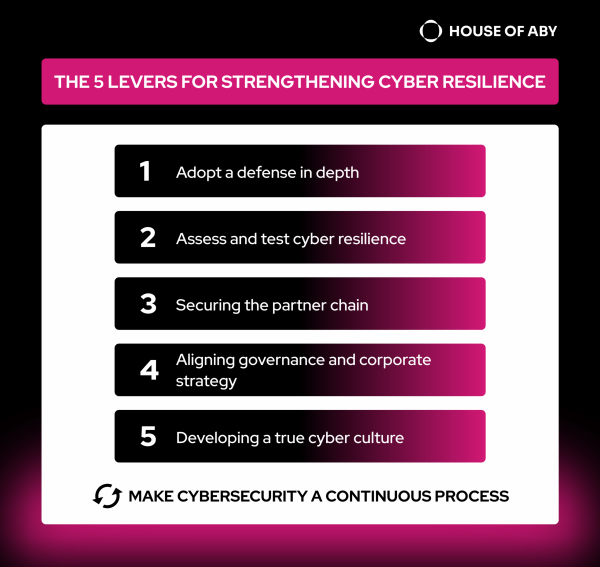
Defense in depth to limit attack impact
The first step is to implement a multi-layered approach combining prevention, detection, and response.
- Prevention: segment networks, strictly limit access, harden configurations, and apply patches without delay.
- Detection: ensure continuous monitoring, use real-time supervision and behavioral detection tools — internally or via an external SOC.
- Response: regularly test incident response plans, train teams in crisis management, and maintain close coordination with national authorities (ANSSI, CNIL, etc.).
This defense-in-depth model minimizes attack impact and ensures quick operational recovery.
→ Recent example: several French industrial groups have adopted Zero Trust Network Access (ZTNA) models, verifying every user and device before granting access.
Endorsed by ANSSI, this approach significantly reduces the risk of lateral movement post-intrusion.
Assessing and testing cyber resilience
Since industrial environments operate continuously, resilience cannot wait for a crisis to be tested. It must be measured, prepared, and strengthened proactively.
1. Analyzing maturity and identifying priorities
A cyber audit is the starting point. It identifies critical assets, assesses compliance with standards (ISO 27001, NIS2…), and measures the actual protection level.
This assessment should rely on a detailed risk map:
- What are the most critical assets?
- Which threats target them?
- Which vulnerabilities could be exploited?
- What would the operational, financial, or reputational impacts be?
This clarity enables effective prioritization and avoids scattered initiatives.
2. Planning investments and actions
Maturity assessment defines a roadmap for continuous improvement, distinguishing between:
- Quick wins: rapid fixes, configuration hardening, targeted awareness campaigns
- Structural actions: network segmentation, BCP/DRP, SOC, cyber governance
Resources should focus on high-impact risks rather than dispersed projects.
3. Testing and strengthening resilience
Regular testing turns theoretical preparedness into real operational reflexes.
Effective exercises include:
- Penetration tests: simulate real attacks to measure system robustness
- Crisis management drills: engage IT, management, and business units to assess collective responsiveness
- Real-world simulations: with specialized partners to test full incident response chains
- Continuous BCP/DRP verification: to ensure rapid restart of critical operations
→ Example: In September 2025, ANSSI, with the Campus Cyber, CESIN, CLUSIF, and CCA, organized REMPAR25, a large-scale national cyber crisis exercise. Over 5,000 participants from 1,000 public and private organizations faced an extreme blackout scenario, testing national coordination and resilience. (Source: ANSSI press release, September 2025)
By combining technical and organizational readiness, companies turn cybersecurity into an embedded, everyday competence.
Securing the partner ecosystem
Recent attacks show that vulnerabilities often lie within suppliers, not core systems. In such interconnected industries, an organization’s security depends on its partners.
Supply chain control requires:
- Regular audits and maturity assessments of providers
- Strict security clauses in contracts
- Controlled information sharing on a need-to-know basis
- Transparent, trust-based partnerships
To combat cascading “rebound” attacks, several industries now collaborate with ANSSI and professional associations to define common cybersecurity frameworks for suppliers.
These collective efforts improve maturity assessment, build trust, and strengthen ecosystem-wide resilience.
Aligning governance with corporate strategy
Cyber strategy success depends on strong executive involvement and cross-functional collaboration.
Cyber risks must be treated as business risks — impacting continuity, reputation, trust, and performance.
Integrated governance fosters trust across departments and partners, embedding cybersecurity into overall corporate strategy.
→ Example: Orange has integrated cybersecurity into its strategic performance indicators, alongside financial and ESG metrics. As outlined in its 2024 integrated report, this approach demonstrates how a large group can turn security into a governance and performance lever at the highest level.
Building a true cyber culture
According to SentinelOne, nearly 90% of cyber incidents stem from human error or negligence. One careless click can trigger a major crisis.
Technology alone is not enough — security depends on collective awareness and responsibility.
Key levers to develop cyber culture:
- Job-specific training: short, role-based modules linking cyber hygiene to daily tasks
- Simulated phishing and feedback: hands-on learning that turns mistakes into progress
- Regular communication: clear, positive messages that maintain vigilance without fear
- Managerial rituals: integrate security into team meetings, onboarding, and reporting
- Visible leadership involvement: lead by example and reward good practices
Training and engaging employees is a high-return investment: it strengthens trust, reduces risk, and makes cybersecurity a shared reflex.
A truly resilient organization relies as much on its people as on its technologies.
Making cybersecurity a continuous process
Cybersecurity is no longer a time-limited project — it’s a continuous improvement cycle.
Regularly tracking progress through indicators, incidents, training, and compliance ensures steady alignment with evolving risks.
The key: combine threat intelligence, lessons learned, and risk reassessment to maintain a high protection level against ever-changing threats.
Ultimately, technical security must rest on strong governance and the commitment of all stakeholders.
By embedding cybersecurity into strategy, culture, and governance, organizations can turn regulatory constraints into drivers of trust and sustainable performance.
Conclusion
Amid escalating threats and increasingly complex industrial environments, cybersecurity has become an issue of continuity and sovereignty.
The most resilient organizations are those that integrate it at every level — from governance to day-to-day operations.
At House of ABY, we work alongside industrial players in sensitive sectors such as nuclear, aerospace, life sciences, and finance. We design and deploy solutions that meet their safety, performance, and resilience needs.
Convinced that security goes beyond technology, we place business risk understanding and sector-specific constraints at the heart of our projects.
Your projects require safety, performance, and trust?
